by rkyadav245833@gmail.com | Feb 15, 2026 | Uncategorized
IntroductionAs the cloud-native landscape continues to evolve, Kubernetes remains the industry standard for container orchestration. With the release of Ubuntu 24.04 LTS (Noble Numbat), DevOps engineers have access to a stable, long-term supported platform for...
by rkyadav245833@gmail.com | Feb 15, 2026 | Uncategorized
Introduction to DevOpsDevOps is more than just a buzzword; it is a cultural shift that bridges the gap between development and operations teams. By integrating these two traditionally siloed departments, organizations can accelerate software delivery, improve...
by rkyadav245833@gmail.com | Feb 15, 2026 | Uncategorized
The Evolving Landscape: Understanding the Future of AIArtificial Intelligence is no longer a concept confined to science fiction; it is the engine driving the next industrial revolution. As we look toward the future of AI, we see a shift from simple task automation to...

by rkyadav245833@gmail.com | Nov 6, 2025 | Uncategorized
The recent Gujarat maternity hospital CCTV hacking case exposed a dark truth — most surveillance systems meant to ensure safety are themselves dangerously insecure. Hackers accessed and sold over 50,000 private video clips from hospital and residential CCTV dashboards...
by rkyadav245833@gmail.com | Jul 16, 2025 | Uncategorized
Got it, let’s dive deeper into the technical aspects of PCAP analysis for network-based attacks. From PCAP to RCA: A Technical Deep Dive into Network Attack Storytelling Understanding the intricate details of a network-based attack requires a meticulous...
by rkyadav245833@gmail.com | Jul 16, 2025 | Uncategorized
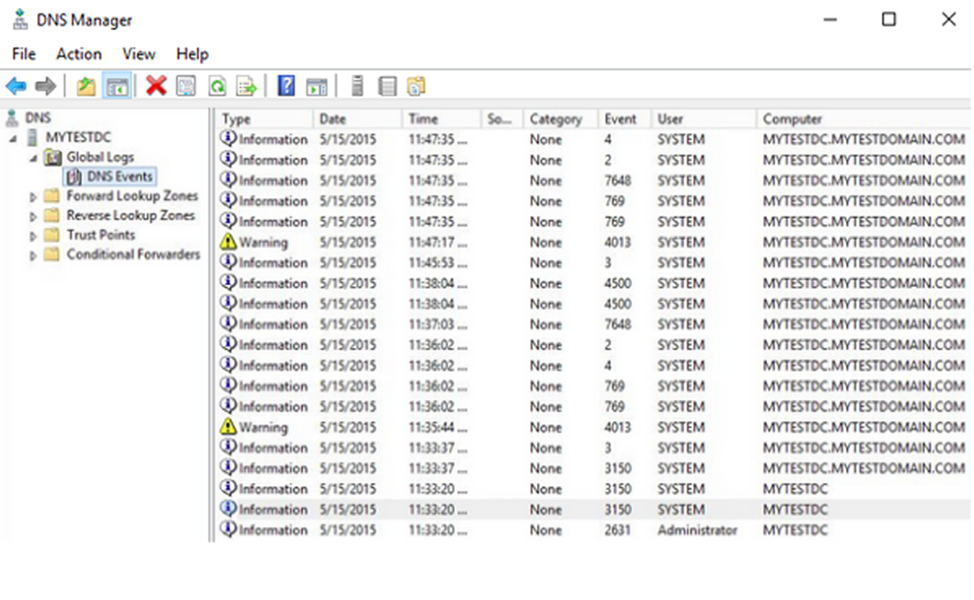
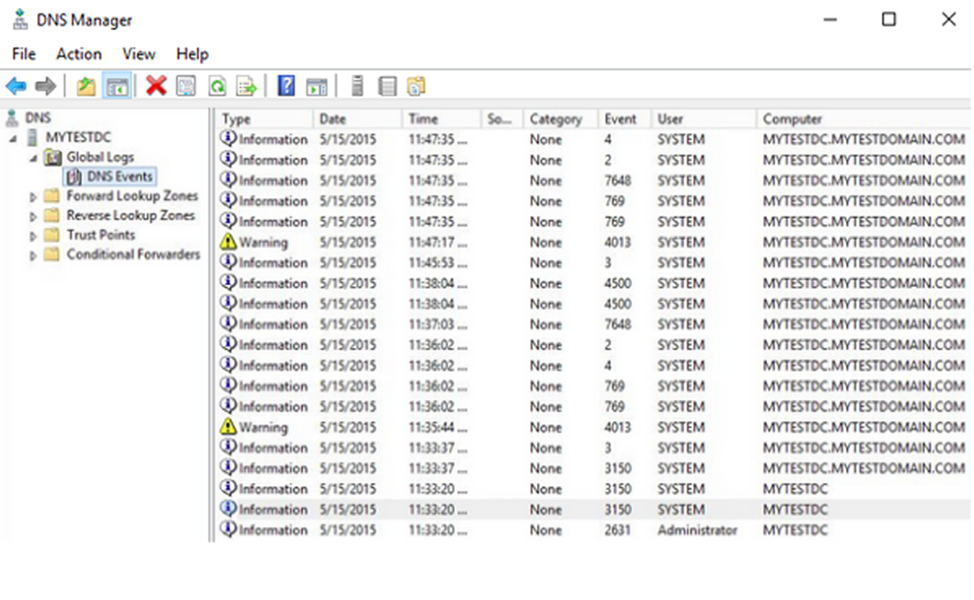
In any Security Operations Center (SOC), Windows Event Logs are one of the most essential and frequently used data sources for threat detection and incident investigation. Whether you’re working in a Tier 1 analyst role or just starting your cybersecurity...